What it is
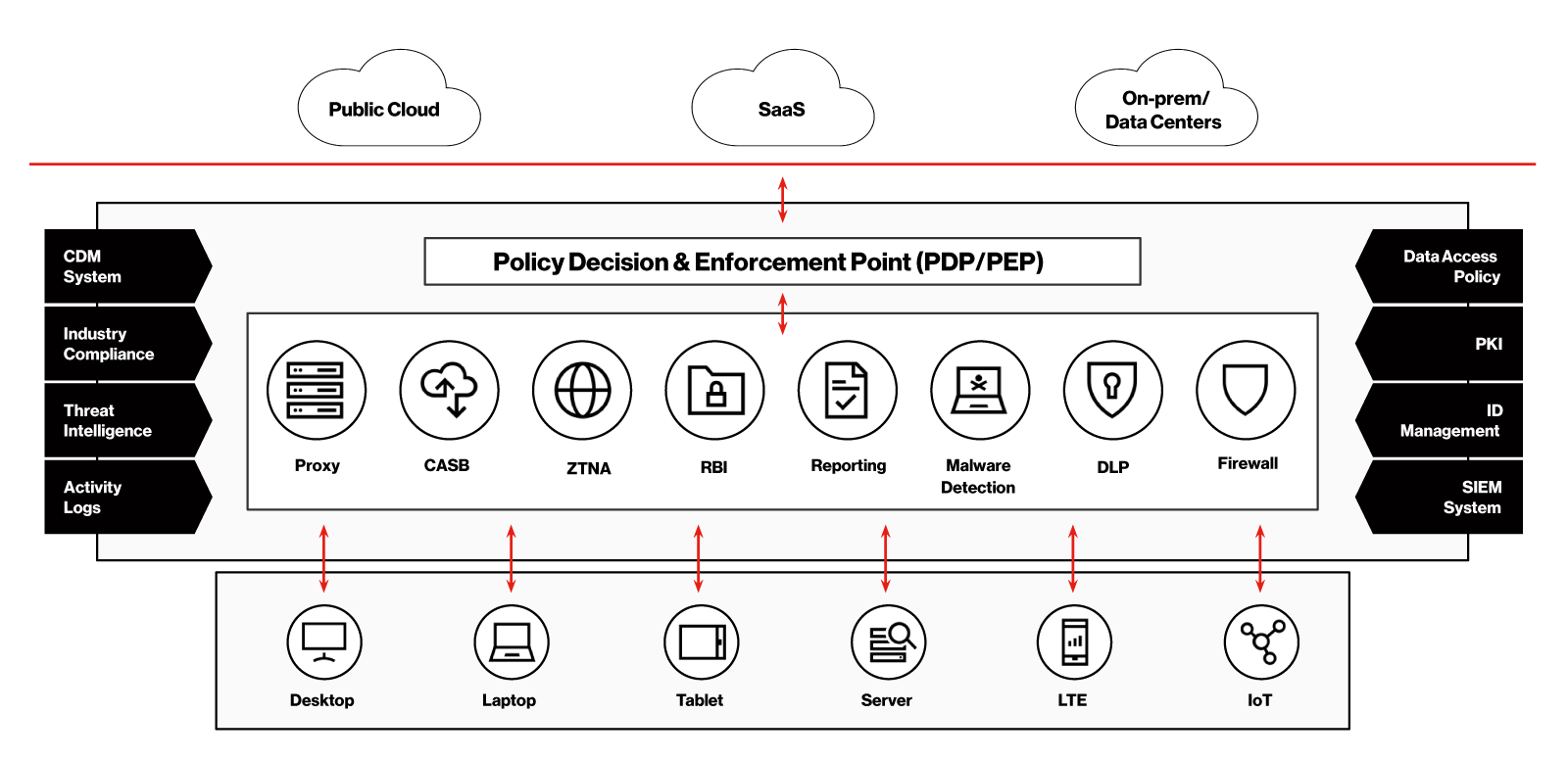
Zero Trust Dynamic Access can block user, app and data attacks, and gives trusted users secure access from virtually anywhere they connect to the network.

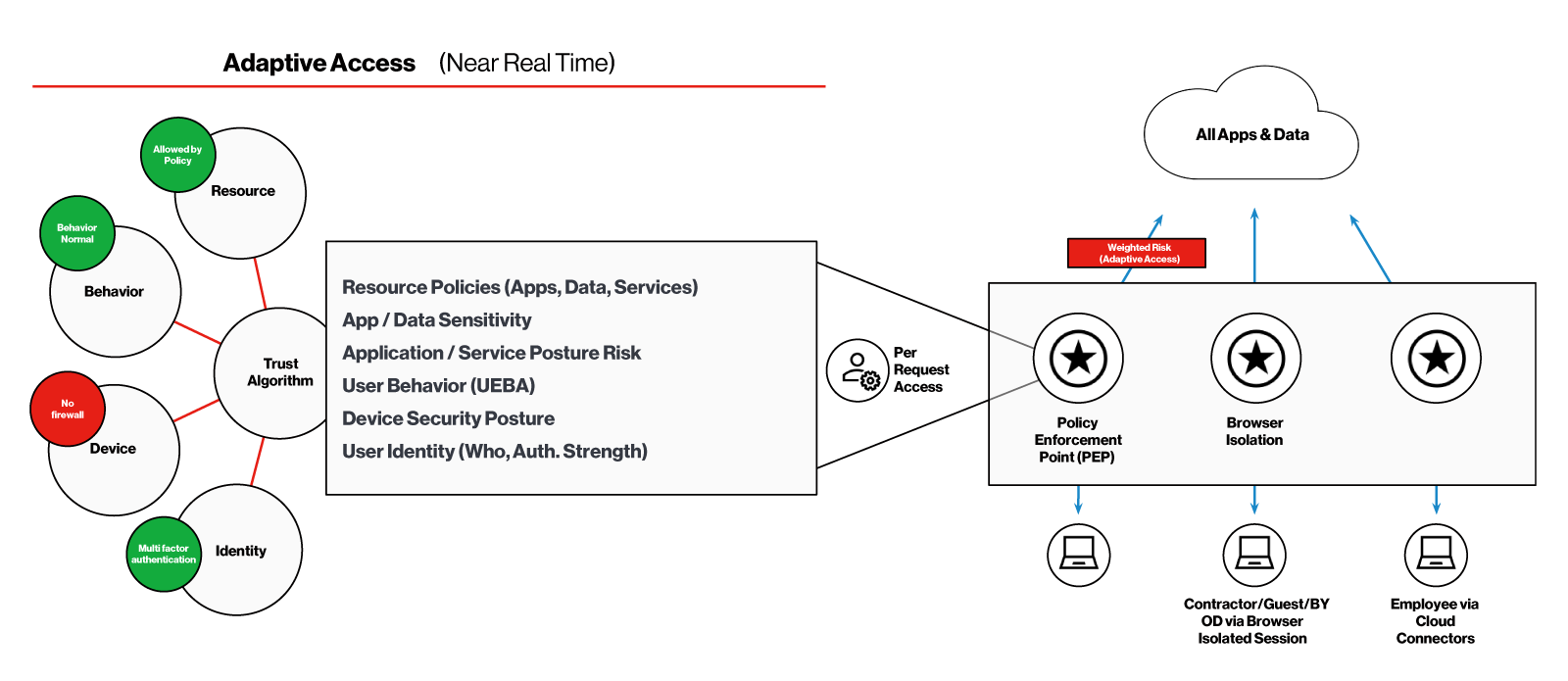
Zero Trust Dynamic Access automatically connects approved and trusted resources by inspecting and authorizing each transaction between users and protected resources.
Transactions are inspected for cloud access security broker (CASB), malware defense and data loss prevention to minimize the risks between authentication and sensitive data access.
The platform continuously makes per-request access decisions using predetermined criteria and role-based access policies each time a transaction to sensitive apps occurs. Doing so helps reduce security risks by blocking access to sensitive data and apps as soon as a device is determined to be infected by malware or ransomware.
Benefits
Features
SSE solution
Provide connectivity and security to both private on-premises resources and public cloud apps for all users regardless of location.
100% inspection
Get peace of mind knowing that Zero Trust Dynamic Access inspects 100% of all traffic that flows through the platform regardless of location.
Industry standard
Use a platform that provides a zero trust edge architecture that’s aligned specifically to the National Institute of Standards (NIST) 800-207 framework and supports IPv6 architecture.
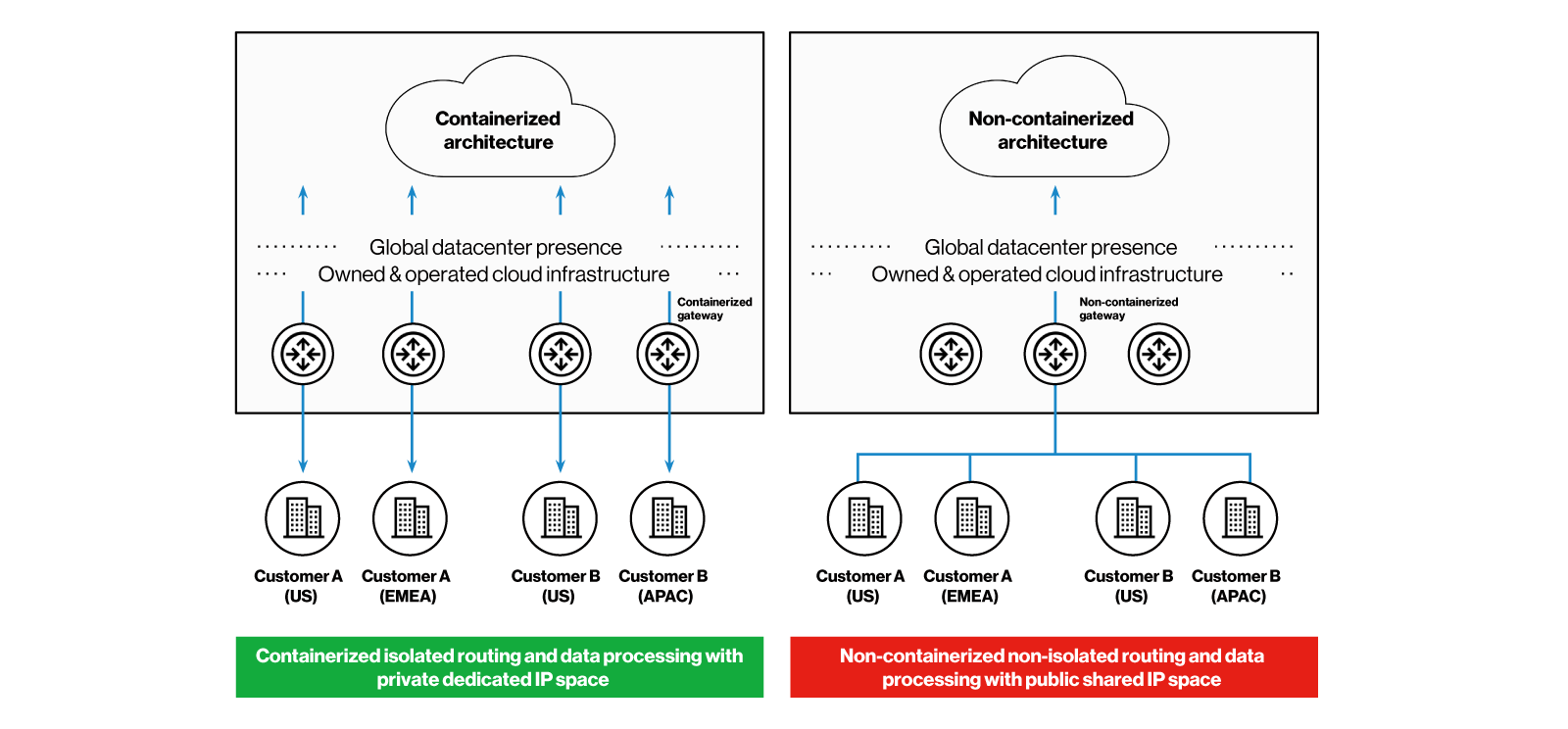
Non-shared containers
Help improve performance, security and compliance with elastic and infinite scale, along with a private dedicated IP space, using non-shared containerized architecture.
Resources
2024 Data Breach Investigations Report
This year, we analyzed a staggering 30,458 real-world security incidents. Download the DBIR to find out more about the cyber threats your organization might be up against.
Transform your Security with Zero Trust Protection
Be proactive in reducing your risk level using planned steps to protect your network resources with a zero trust architecture. Learn how Verizon can support your zero trust journey and how Zero Trust Dynamic Access can augment your security team’s approach.
Transform Your Security with Zero Trust Protection webinar
Find out what zero trust is, the benefits of using zero-trust architecture and how Verizon Zero Trust Dynamic Access can help you create a zero-trust plan.
Establishing a Zero Trust Model in IoT Environments paper
Learn the common Internet of Things (IoT) cyberthreats, how to categorize them and how to address them using a four-step process based on a zero-trust capability mode.
Zero Trust Dynamic Access fact sheet
Discover how to help prevent breaches by making apps, data and services inaccessible while allowing trusted users to securely connect to protected resources.
FAQs
Zero Trust Network Access can help improve network performance and latency for all users, including remote workers. It supports controls over which applications can be accessed, while enhancing security with continuous authentication verification. Zero Trust Network Access acts similar to a VPN, but provides a much better user experience because it’s always on—no logging in required.