Phishing
Stay a step ahead of the scammers. Educate yourself on some of the most common frauds and scams.
What is phishing?
Phishing is first and foremost a cybercrime. In a phishing scam, a target is contacted by email, telephone or text message by someone posing as a close personal contact or on behalf of a legitimate institution. The objective is to get people to reveal sensitive data such as their account numbers, home address, banking/credit card details and usernames/passwords. The information is then used to access important accounts and can result in identity theft and financial loss.
What are the types of phishing attacks?
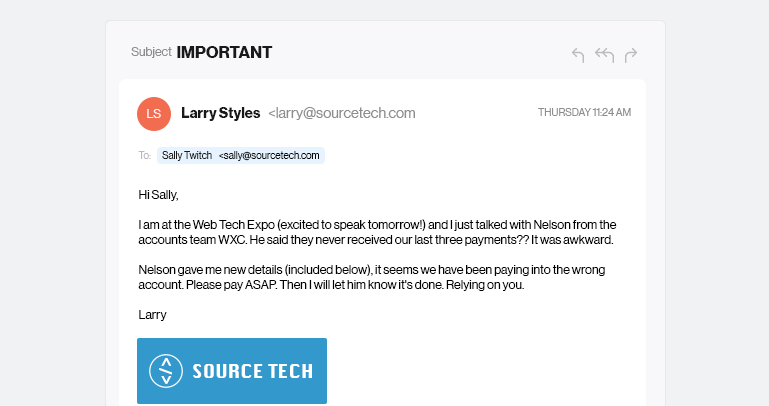
See This Example Of A Spear Phishing Email
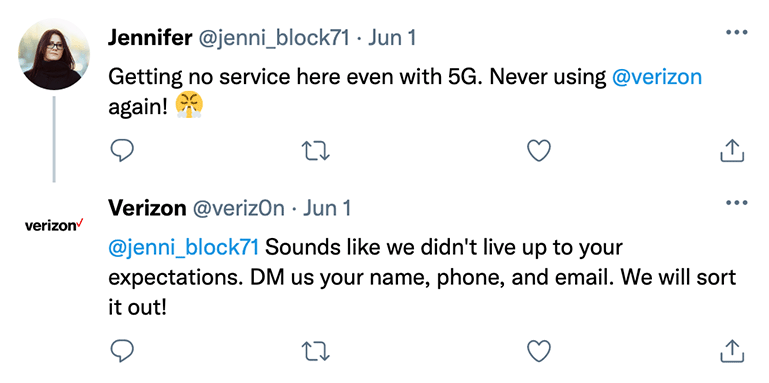
Here Is An Example Of How Fraudsters Use Fake Accounts.
- Email Phishing aka "deceptive phishing" refers to a fraudster who creates and sends deceptive emails with the goal of obtaining sensitive financial and personal information. The emails are typically designed to look exactly like the ones sent by legitimate companies. These emails contain links that often lead to “fake” or “spoofed” websites where visitors are asked to provide personal information.
- Trap Phishing is largely based on the mistakes of a company's IT (Information Technology) teams. Hackers and cyber-criminals are always on the lookout for security faults and vulnerabilities within a company's web ecosystem. Verizon takes extraordinary measures to prevent this from happening to its customers and the customers of our business clients.
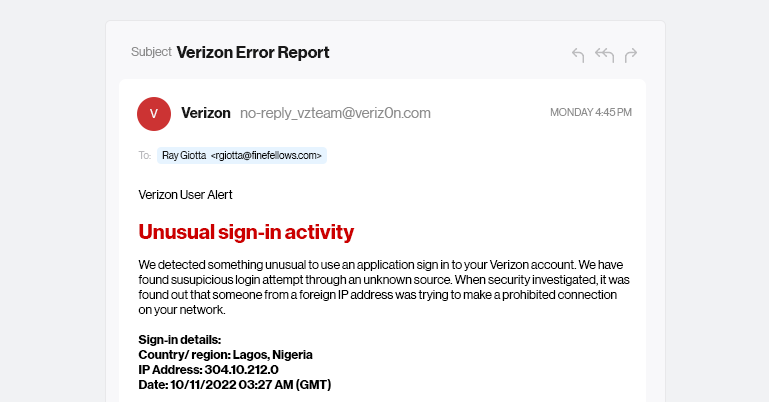
- Spear Phishing targets a specific group or type of individual such as a company’s system administrator. See this example of a spear phishing email. Note the attention paid to the industry in which the recipient works, the download link the victim is asked to click and the immediate response the request requires. The spear phisher typically already has information about the admin, such as name, place of employment, job title, email address and information about their role in the company.
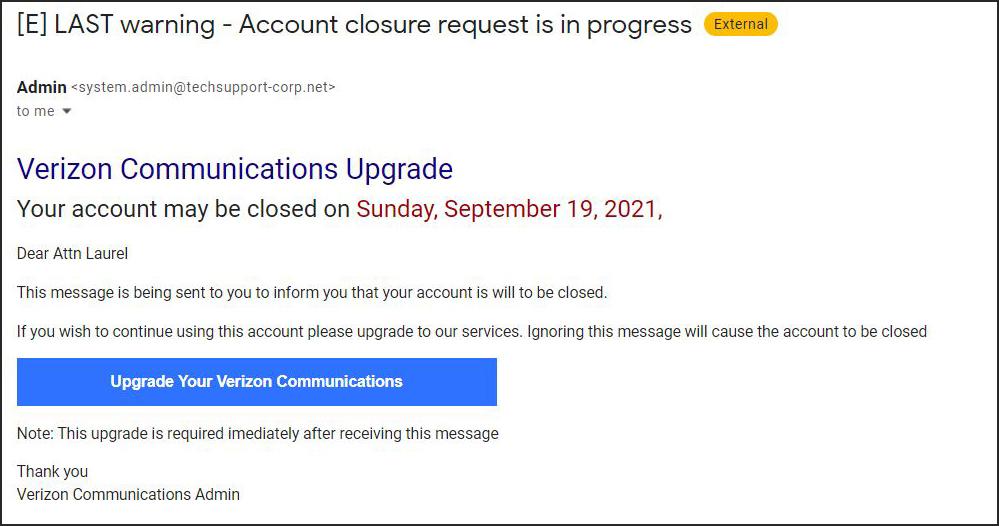
- Angler Phishing is a new kind of phishing which uses social media to lure users to fake URLs, cloned websites, other posts/tweets and IMs that can be used to persuade people to divulge sensitive information or download malware. Anglers set up fake social media accounts that closely resemble popular brands and respond to social posts often requesting user information. Here is an example of how fraudsters use fake accounts.
- Whaling is an even more targeted type of phishing that goes after “whales,” a term coined by the financial industry, which refers to CEOs, CFOs or other high level executives. A whaling email might ask the executive to update information or state that the company is facing legal consequences that must be remedied immediately by clicking on a link.
- Voice Phishing, aka "Vishing" has the same purpose as other types of phishing attacks. The attackers are still after your sensitive, personal or corporate information, but this attack is accomplished through a voice call. Hence the “v” rather than the “ph” in the name. Once a visher gets a victim on the phone, they make a strong appeal to the victim’s human instinct of trust, fear, greed or the desire to help.
- Text Phishing, aka "Smishing" is an attack that uses text messaging or short message service (SMS) to execute the attack. A common smishing technique is to deliver a message to a cell phone through SMS that contains a clickable link or a return phone number. Go to our smishing webpage for more in-depth information and details as this type of scam is on the rise.
- Pharming involves hijacking the user’s browsers settings to show suspicious pop ups asking the user to click a link that then downloads malicious code executed on the victim's device to redirect to an attacker-controlled website. In order to avoid being ‘pharmed’, you should never click links from pop ups, always manually type the official domain of a website into your browser.
How to identify phishing emails and websites.
Phishing messages vary in form and content but here are some important guidelines and examples on how to identify phishing scams.
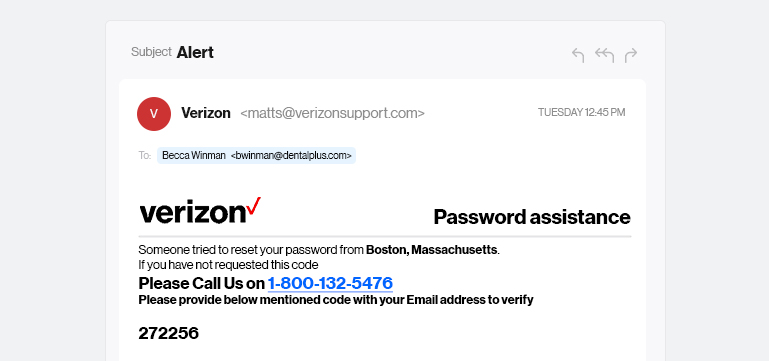
The phishing message is not meaningful to you. The message appears to be random and unprompted, and doesn’t relate to anything you did recently online. For example, an email may say ‘thank you for paying your bill online - please verify the following information’ when, in fact, you did not just pay your bill.
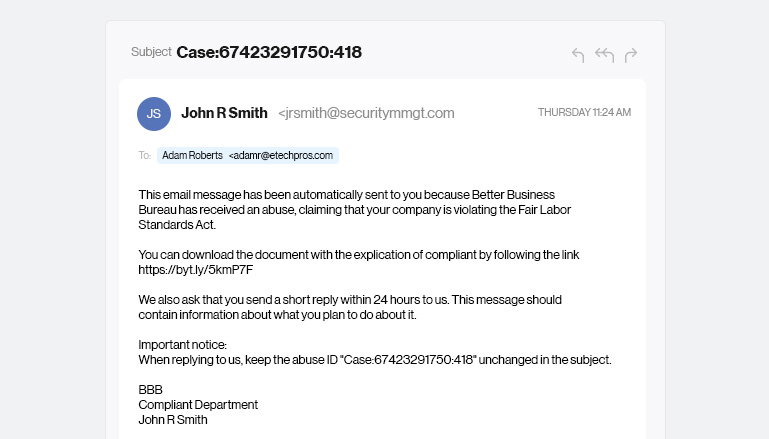
The phishing email is sent from a public email domain or illegitimate domain. Look at the end of the sender's email. Is it coming from a legitimate domain? All companies use very specific domains in their email address. It is unlikely a large company will send emails from @gmail.com. Phishers will try to trick you by using the company name before the domain. Remember the most important part of the email address is the last part.
The email domain is misspelled. Phishers will try to get real close to the company's legal domain. E.g., Verizon-Services@verzon.com Notice the email domain is missing one small character. Many companies have taken precautions to protect its customers against this, by buying all misspelled domain names so scammer’s can’t use them.
The email includes attachments. You can spot a phishing email if it contains an attachment that you didn't specifically request and the file name looks odd, or ends in .zip or .exe. These attachments often contain malware, which once downloaded can provide the scammer with access to sensitive information on the user's PC.
As for links, scammers are getting clever and embedding links in buttons or using short URLs like bit.lys. When you see a button or other stylized link, simply hover over the link with your mouse and the URL will appear in the lower left corner of your screen. On a mobile device, press on the link and a pop-up will appear that shows the link URL.
The message creates a sense of urgency, contains typos or just looks “off.” The email uses language that attempts to invoke fear if the recipient doesn’t “act now.” Examples include:
- We recently reviewed your account, and we need more information to help us provide you with secure service.
- We have reason to believe that your account was accessed by a third party. To help prevent this from happening again just confirm your identity and location.
- Your online account preferences were changed by someone else. We have disabled most of the accessible features of your account. You have to login from your device in order to reactivate your online functions again.
- Thanks for paying your bill, here’s your free gift!
How to report phishing scams to Verizon.
Phishing scams are very common and you are likely to receive them often. If you receive a suspicious email or text message claiming to be from Verizon, please forward it to us right away. You can forward the email to phishing@verizon.com or report a suspicious text to S-P-A-M (7726). You can also report it to the Federal Trade Commission. Verizon will never ask for personal or account information by email or text message. If you receive a spam email or text message you should send it to Verizon then DELETE IT IMMEDIATELY.
To view Verizon Specific examples of phishing, visit our support section.
How to protect yourself from phishing attempts.
The best defense against phishing is to educate yourself on best practices and research available tools that can help you manage spam emails.
- Email filtering. Most popular email service providers, such as gmail, yahoo, AOL and hotmail offer ways to set up filters to block emails coming from specific domains. Verizon offers ways to add spam blocks via its My Verizon portal. Follow these instructions on how to Add/Remove Spam Blocks on My Verizon.
- Use a secure web browser. A safe web browser such as Google, Chrome or Safari add extra security measures to help prevent unauthorized third party activity while you surf the web. Also, be mindful of URL structure– when clicking on any link–make sure it uses https:// protocols - the ‘s’ means the URL is secure.
- Install anti-phishing and account security tools. Most popular internet browsers such as Google Chrome have free anti-phishing tools and plug-ins. You can also use a reputable VPN service or enable two-factor authentication on accounts that offer it.
- Never click on links from pop-ups. In order to avoid being ‘pharmed’, you should never click links from pop ups, always manually type the official domain of a website into your browser.
- Never connect to a public Wi- Fi hotspot without VPN.