What it is
Stay productive and protected with application and device security services that include data encryption, trusted user authentication components and automated provisioning.

Dynamic protection
The Verizon IoT Security Credentialing solution integrates security with your IoT services, and only allows known and trusted devices in your IoT solution to connect to your network and resources.
Trusted identity loop
- Only authentic firmware, applications and configurations can be deployed and installed on an embedded SIM
- Creates a trusted ecosystem that is established by making Roots of Trust and certificates for trusted users and devices
Insights
Our IoT security solutions are created with insights gained from more than a dozen years analyzing over 200,000 security incidents around the globe.
Resources
2025 Data Breach Investigations Report
Today's threat landscape is shifting. Get the latest updates on real-world breaches and help safeguard your organization from cybersecurity attacks.
2025 Mobile Security Index
Learn about the latest mobile security threats and how to help protect your organization.
Today’s IoT demands intelligent security.
Learn how IoT Security Credentialing helps keep bad things from happening to good IoT solutions.
FAQs
It is important to design security into your IoT solutions from the start where possible. IoT ecosystems should cater for the following basic security tenets:
Availability—Ensuring connectivity between endpoints and their respective services allows for secure monitoring and management of the devices and enables secure firmware updates.
Identity—Authenticate endpoints, services, firmware updates and the customer or end user operating the endpoint. Use secure elements such as eSIM and TPMs for cryptographic key management. Use unique keys, certificates and roots of trust to strongly identify and authenticate devices.
Privacy—Reduce the potential for harm to individual end users by enabling privacy-preserving techniques such as encryption and unique identities.
Security—Ensure that system integrity can be verified, tracked and monitored.
Businesses depend on an ever-increasing number of smart technologies to harness the potential innovations and benefits of connectivity. With this proliferation of smart devices and endpoints comes an increased risk of exposure to fraud and attack. It is essential that security is adequately addressed as part of any IoT service or solution to ensure compliance, safety and security for consumers and enterprises.
IoT devices can range from lightweight devices with very low power requirements and storage and processing capabilities to more complex endpoints with persistent connectivity and the ability to utilize more comprehensive security capabilities. Such a heterogeneous environment brings with it security challenges, as there is no "one size fits all."
Endpoint security relates to the practice of preventing endpoints or entry points of end-user or enterprise physical devices—such as IoT devices, IoT gateways, desktops, laptops and mobile devices—from being exploited by malicious actors and campaigns. Endpoint security is one aspect that should be considered in the context of the overall enterprise security strategy. The key to managing and reducing cyberthreats related to endpoints is to have strong device-management and threat-defense capabilities in place. Advanced endpoint identity, detection and protection solutions can help you keep your policies aligned while helping prevent malware, ransomware and other dangerous exploits from infiltrating your business.
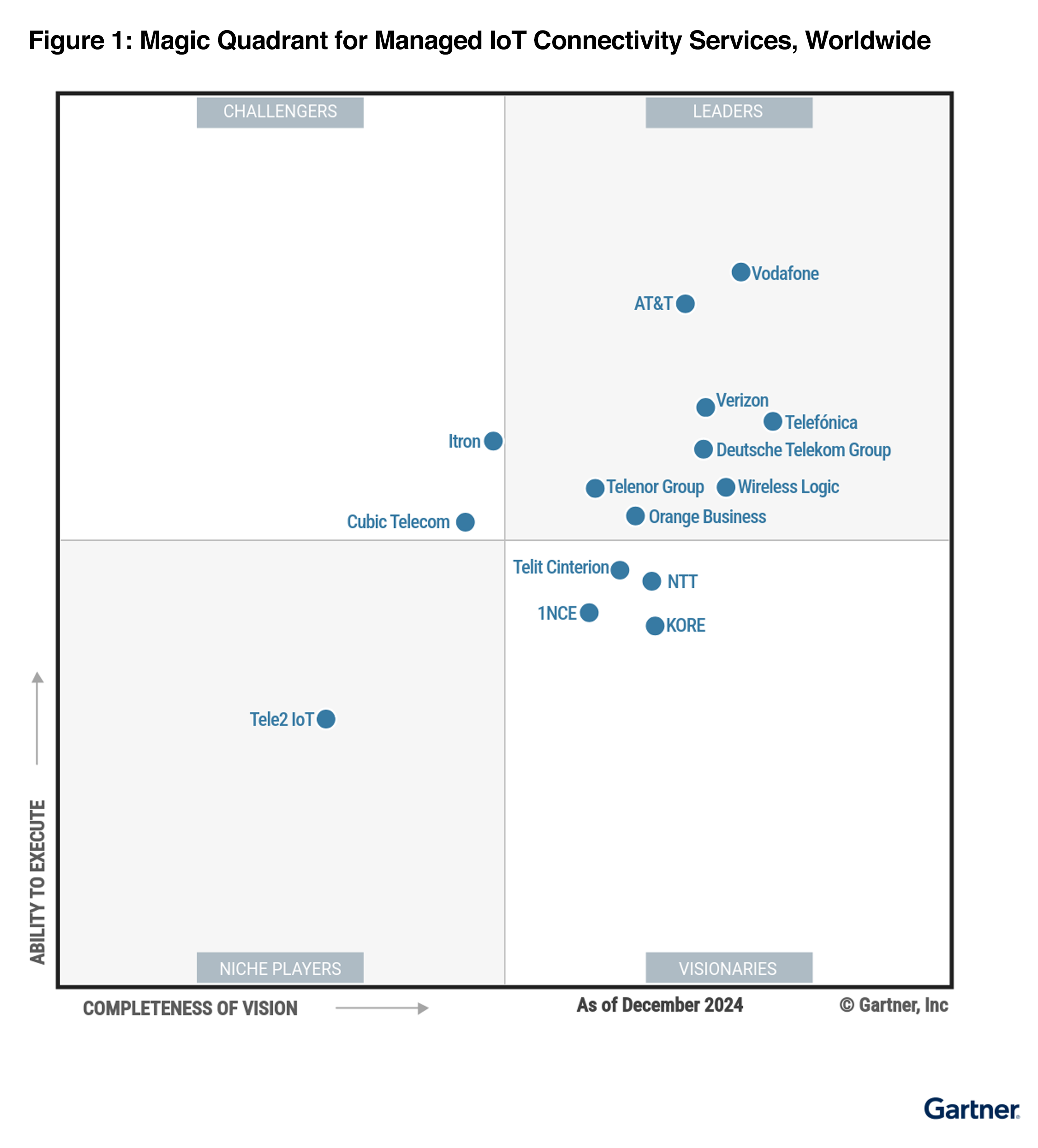
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.