2026 Data Breach Investigations Report
Turn global breach insights into a stronger, more proactive defense for your organization.
Key resources
2026 DBIR
Access the data-driven insights you need to help counter AI-augmented attacks, navigate shifting financial pressure and defend your organization against today’s threats.
2026 Breach Impact Study
See the real cost of a breach. Get the facts you need to make smarter security investments and help protect your bottom line.
Coming soon
Top takeaways
Cybersecurity is constantly evolving. Here are the top takeaways from this year’s report and what they can mean for your business.
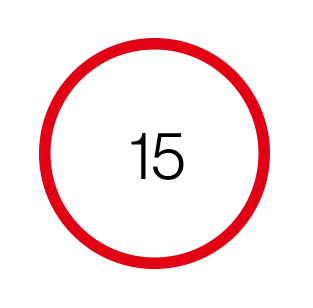
of breaches now start with software vulnerabilities, beating stolen passwords as the top way attackers get in. Hackers are shifting their focus from tricking people to exploiting systems.
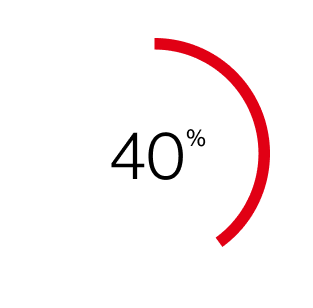
of all breaches now involve ransomware, but payouts are shrinking. Even as ransom amounts decrease, businesses are frequently choosing not to pay.
Watch the webinars
On demand Beyond the Breach:
Deconstructing the 2026 Data Breach Investigations Report
Go beyond the data and get insights directly from the DBIR authors. Sign up to get a firsthand look at how generative AI is augmenting attacks, analyze the impact of shifting financial pressures and learn how to help protect your infrastructure against today’s most prevalent threats.
Customer success story
Explore the archive
2025 DBIR
Get updates on real-world breaches and help safeguard your organization from cybersecurity attacks.
2024 DBIR
Learn how to prepare for cybersecurity threats, no matter the size of your organization. Review real-world breaches to help evaluate potential updates to your security plan.
FAQs
The DBIR is an annual report on cybersecurity analyzing real-world data breaches—how they happen, who’s behind them, and how businesses can stay protected. Using global data, it provides key insights to help companies stay ahead of cyber threats. It acts as a vital cybersecurity risk management report for businesses of all sizes.
Our data is contributed by a wide range of organizations, including domestic and international law enforcement, forensic firms, law firms, cyber insurers, cybersecurity industry sharing groups, and our own Verizon Threat Research Advisory Center (VTRAC) caseload. Each year, the DBIR timeline for in-scope incidents is from November 1 of one calendar year through October 31 of the next calendar year. Thus, the incidents described in the 2026 edition took place between November 1, 2024, and October 31, 2025.
While daily data breach news today fluctuates, the annual DBIR report aggregates and analyzes this data over a 12-month period to identify overarching trends. Our data breach report provides the definitive, data-backed context needed to understand the daily headlines and navigate the complex threat landscape.
No security strategy is foolproof, but businesses can help reduce risk by:
- Using multifactor authentication (MFA) to block unauthorized access
- Keeping software updated to fix security gaps
- Training employees to spot phishing and threats
- Encrypting sensitive data for added protection
- Testing security defenses regularly
- Having an incident response plan in place
By detailing the anatomy of thousands of attacks, the DBIR report helps organizations understand what to look for when conducting their own internal audits. It provides a reliable benchmark for cybersecurity incident reporting, helping security teams refine their incident response procedures to ensure compliance and readiness.
Cyber threats evolve rapidly. Utilizing an authoritative cybersecurity incident report like the DBIR allows your organization to align its defenses with the most current tactics used by cybercriminals. It serves as a foundational tool for executive leadership and IT teams alike to prioritize security investments and validate their data breach reporting frameworks.
Based on the data breach 2026 threat landscape, the most frequent causes continue to heavily involve the human element—including social engineering, phishing, and stolen credentials—as well as the exploitation of software vulnerabilities and ransomware attacks. You can explore the complete data breach investigations and statistical breakdowns by industry within the full report.